SIST EN 419241-1:2018
(Main)Trustworthy Systems Supporting Server Signing - Part 1: General System Security Requirements
Trustworthy Systems Supporting Server Signing - Part 1: General System Security Requirements
1.1 General
This document specifies security requirements and recommendations for Trustworthy Systems Supporting Server Signing (TW4S) that generate digital signatures.
The TW4S is composed at least of one Server Signing Application (SSA) and one Signature Creation Device (SCDev) or one remote Signature Creation Device.
A remote SCDev is a SCDev extended with remote control provided by a Signature Activation Module (SAM) executed in a tamper protected environment. This module uses the Signature Activation Data (SAD), collected through a Signature Activation Protocol (SAP), in order to guarantee with a high level of confidence that the signing keys are used under sole control of the signer.
The SSA uses a SCDev or a remote SCDev in order to generate, maintain and use the signing keys under the sole control of their authorized signer. Signing key import from CAs is out of scope.
So when the SSA uses a remote SCDev, the authorized signer remotely controls the signing key with a high level of confidence.
A TW4S is intended to deliver to the signer or to some other application, a digital signature created based on the data to be signed.
This standard:
- provides commonly recognized functional models of TW4S;
- specifies overall requirements that apply across all of the services identified in the functional model;
- specifies security requirements for each of the services identified in the TW4S;
- specifies security requirements for sensitive system components which may be used by the TW4S.
This standard is technology and protocol neutral and focuses on security requirements.
1.2 Outside of the scope
The following aspects are considered outside of the scope of this document:
- other trusted services that may be used alongside this service such as certificate issuance, signature validation service, time-stamping service and information preservation service;
- any application or system outside of the TW4S (in particular the signature creation application including the creation of advanced signature formats);
- signing key and signing certificate import from CAs;
- the legal interpretation of the form of signature (e.g. electronic signature, electronic seal, qualified or otherwise).
1.3 Audience
This standard specifies security requirements that are intended to be followed by:
- providers of TW4S systems;
- Trust Service Providers (TSP) offering a signature creation service.
Vertrauenswürdige Systeme, die Serversignaturen unterstützen - Teil 1: Allgemeine Systemsicherheitsanforderungen
Systèmes fiables de Serveur de Signature électronique - Partie 1: Exigences de sécurité générales du système
Zaupanja vredni sistemi, ki podpirajo strežniško podpisovanje - 1. del: Splošne varnostne zahteve sistema
Področje uporabe predlaganega 1. dela standarda 419241 (Varnostne zahteve) zajema varnostne zahteve in priporočila za zaupanja vredne sisteme, ki podpirajo strežniško podpisovanje (TW4S) in generirajo digitalne podpise. Te digitalne podpise ustvarja oddaljeno sredstvo za elektronsko podpisovanje (rSCDev). Oddaljeno sredstvo za elektronsko podpisovanje je sredstvo za elektronsko podpisovanje (SCDev), ki uporablja varne kanale za elektronsko komunikacijo z namenom zagotavljanja zanesljivega okolja za elektronsko podpisovanje, ki je pod izključnim nadzorom podpisnika. Ta predlagani 1. del standarda 419241 bo obstoječi standard CEN/TS 419241 prilagodil zahtevam nove Uredbe EU št. 910/2014 in TS pretvoril v EN.
General Information
- Status
- Published
- Publication Date
- 04-Sep-2018
- Technical Committee
- ITC - Information technology
- Current Stage
- 6060 - National Implementation/Publication (Adopted Project)
- Start Date
- 02-Aug-2018
- Due Date
- 07-Oct-2018
- Completion Date
- 05-Sep-2018
Relations
- Replaces
SIST-TS CEN/TS 419241:2014 - Security Requirements for Trustworthy Systems Supporting Server Signing - Effective Date
- 01-Oct-2018
Overview
EN 419241-1:2018 (CEN) defines security requirements and recommendations for Trustworthy Systems Supporting Server Signing (TW4S) - server-side systems that generate digital signatures. The standard is technology- and protocol-neutral and focuses on ensuring that signing keys are generated, maintained and used under the sole control of the authorized signer. It covers server signing architectures that include at least a Server Signing Application (SSA) and a Signature Creation Device (SCDev) or a remote SCDev (extended with a Signature Activation Module (SAM)). Remote control is enabled using Signature Activation Data (SAD) exchanged via a Signature Activation Protocol (SAP). Importantly, importing signing keys from Certification Authorities (CAs) is out of scope.
Key topics and requirements
- Functional models: Common architectures for TW4S, including SSA + SCDev and remote SCDev scenarios.
- Sole control assurance: Mechanisms and assurance levels to guarantee that signing keys are used only under signer control.
- Remote signature activation: Requirements for SAM, SAD and SAP to securely support remote use of SCDev in a tamper-protected environment.
- Core security domains:
- Management and governance (security policy, roles, responsibilities)
- System and operations (secure deployment, hardening, change control)
- Identification and authentication (signer authentication mechanisms and electronic identification means)
- Key management (generation, storage, lifecycle for signing keys and cryptographic modules)
- Access control, auditing and archiving (logging, non-repudiation support, retention)
- Backup and recovery
- Sensitive components: Security requirements for components such as the SAM, SCDev and cryptographic modules.
- Out of scope: CA certificate issuance, signature validation, timestamping, preservation services, and legal classification of signature form.
Practical applications
- Implementation guidance for Trust Service Providers (TSPs) offering remote signature creation services.
- Specification baseline for developers of server signing platforms, cloud-based digital signature services, and managed signing solutions.
- Input for security architects and auditors to assess compliance with eIDAS-aligned best practices for remote signing.
- Foundation for producing protection profiles or certification artifacts (e.g., QSCD-related profiles) for server-side signing components.
Who should use this standard
- TSPs and service operators deploying server-side signature solutions
- Solution architects, security engineers and product vendors building SSA, SCDev, SAM or remote signing services
- Auditors and conformity assessors evaluating eIDAS-relevant server signing deployments
Related standards
- ETSI EN 319 401 (trust service general requirements) - recommended complement
- EN 419241-2 (protection profile for QSCD for server signing) - companion part in the same series
Keywords: EN 419241-1:2018, server signing, trustworthy systems, remote signature creation, eIDAS, SCDev, SAM, SAD, SAP, Trust Service Provider (TSP), digital signature.
Frequently Asked Questions
SIST EN 419241-1:2018 is a standard published by the Slovenian Institute for Standardization (SIST). Its full title is "Trustworthy Systems Supporting Server Signing - Part 1: General System Security Requirements". This standard covers: 1.1 General This document specifies security requirements and recommendations for Trustworthy Systems Supporting Server Signing (TW4S) that generate digital signatures. The TW4S is composed at least of one Server Signing Application (SSA) and one Signature Creation Device (SCDev) or one remote Signature Creation Device. A remote SCDev is a SCDev extended with remote control provided by a Signature Activation Module (SAM) executed in a tamper protected environment. This module uses the Signature Activation Data (SAD), collected through a Signature Activation Protocol (SAP), in order to guarantee with a high level of confidence that the signing keys are used under sole control of the signer. The SSA uses a SCDev or a remote SCDev in order to generate, maintain and use the signing keys under the sole control of their authorized signer. Signing key import from CAs is out of scope. So when the SSA uses a remote SCDev, the authorized signer remotely controls the signing key with a high level of confidence. A TW4S is intended to deliver to the signer or to some other application, a digital signature created based on the data to be signed. This standard: - provides commonly recognized functional models of TW4S; - specifies overall requirements that apply across all of the services identified in the functional model; - specifies security requirements for each of the services identified in the TW4S; - specifies security requirements for sensitive system components which may be used by the TW4S. This standard is technology and protocol neutral and focuses on security requirements. 1.2 Outside of the scope The following aspects are considered outside of the scope of this document: - other trusted services that may be used alongside this service such as certificate issuance, signature validation service, time-stamping service and information preservation service; - any application or system outside of the TW4S (in particular the signature creation application including the creation of advanced signature formats); - signing key and signing certificate import from CAs; - the legal interpretation of the form of signature (e.g. electronic signature, electronic seal, qualified or otherwise). 1.3 Audience This standard specifies security requirements that are intended to be followed by: - providers of TW4S systems; - Trust Service Providers (TSP) offering a signature creation service.
1.1 General This document specifies security requirements and recommendations for Trustworthy Systems Supporting Server Signing (TW4S) that generate digital signatures. The TW4S is composed at least of one Server Signing Application (SSA) and one Signature Creation Device (SCDev) or one remote Signature Creation Device. A remote SCDev is a SCDev extended with remote control provided by a Signature Activation Module (SAM) executed in a tamper protected environment. This module uses the Signature Activation Data (SAD), collected through a Signature Activation Protocol (SAP), in order to guarantee with a high level of confidence that the signing keys are used under sole control of the signer. The SSA uses a SCDev or a remote SCDev in order to generate, maintain and use the signing keys under the sole control of their authorized signer. Signing key import from CAs is out of scope. So when the SSA uses a remote SCDev, the authorized signer remotely controls the signing key with a high level of confidence. A TW4S is intended to deliver to the signer or to some other application, a digital signature created based on the data to be signed. This standard: - provides commonly recognized functional models of TW4S; - specifies overall requirements that apply across all of the services identified in the functional model; - specifies security requirements for each of the services identified in the TW4S; - specifies security requirements for sensitive system components which may be used by the TW4S. This standard is technology and protocol neutral and focuses on security requirements. 1.2 Outside of the scope The following aspects are considered outside of the scope of this document: - other trusted services that may be used alongside this service such as certificate issuance, signature validation service, time-stamping service and information preservation service; - any application or system outside of the TW4S (in particular the signature creation application including the creation of advanced signature formats); - signing key and signing certificate import from CAs; - the legal interpretation of the form of signature (e.g. electronic signature, electronic seal, qualified or otherwise). 1.3 Audience This standard specifies security requirements that are intended to be followed by: - providers of TW4S systems; - Trust Service Providers (TSP) offering a signature creation service.
SIST EN 419241-1:2018 is classified under the following ICS (International Classification for Standards) categories: 35.030 - IT Security. The ICS classification helps identify the subject area and facilitates finding related standards.
SIST EN 419241-1:2018 has the following relationships with other standards: It is inter standard links to SIST-TS CEN/TS 419241:2014. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
SIST EN 419241-1:2018 is associated with the following European legislation: EU Directives/Regulations: 910/2014; Standardization Mandates: M/460. When a standard is cited in the Official Journal of the European Union, products manufactured in conformity with it benefit from a presumption of conformity with the essential requirements of the corresponding EU directive or regulation.
SIST EN 419241-1:2018 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
2003-01.Slovenski inštitut za standardizacijo. Razmnoževanje celote ali delov tega standarda ni dovoljeno.Zaupanja vredni sistemi, ki podpirajo strežniško podpisovanje - 1. del: Splošne varnostne zahteve sistemaVertrauenswürdige Systeme, die Serversignaturen unterstützen - Teil 1: Allgemeine SystemsicherheitsanforderungenSystèmes fiables de Serveur de Signature électronique - Partie 1: Exigences de sécurité générales du systèmeTrustworthy Systems Supporting Server Signing - Part 1: General System Security Requirements35.030Informacijska varnostIT SecurityICS:Ta slovenski standard je istoveten z:EN 419241-1:2018SIST EN 419241-1:2018en,fr,de01-oktober-2018SIST EN 419241-1:2018SLOVENSKI
STANDARDSIST-TS CEN/TS 419241:20141DGRPHãþD
EUROPEAN STANDARD NORME EUROPÉENNE EUROPÄISCHE NORM
EN 419241-1
July
t r s z English Version
Trustworthy Systems Supporting Server Signing æ Part
sã General System Security Requirements Systèmes fiables de serveur de signature électronique æPartie
sã Exigences de sécurité générales du système
Vertrauenswürdige Systemeá die Serversignaturen unterstützen æ Teil
sã Allgemeine Systemsicherheitsanforderungen This European Standard was approved by CEN on
u r April
t r s zä
egulations which stipulate the conditions for giving this European Standard the status of a national standard without any alterationä Upætoædate lists and bibliographical references concerning such national standards may be obtained on application to the CENæCENELEC Management Centre or to any CEN memberä
translation under the responsibility of a CEN member into its own language and notified to the CENæCENELEC Management Centre has the same status as the official versionsä
CEN members are the national standards bodies of Austriaá Belgiumá Bulgariaá Croatiaá Cyprusá Czech Republicá Denmarká Estoniaá Finlandá Former Yugoslav Republic of Macedoniaá Franceá Germanyá Greeceá Hungaryá Icelandá Irelandá Italyá Latviaá Lithuaniaá Luxembourgá Maltaá Netherlandsá Norwayá Polandá Portugalá Romaniaá Serbiaá Slovakiaá Sloveniaá Spainá Swedená Switzerlandá Turkey and United Kingdomä
EUROPEAN COMMITTEE FOR STANDARDIZATION COMITÉ EUROPÉEN DE NORMALISATION EUROPÄISCHES KOMITEE FÜR NORMUNG
CEN-CENELEC Management Centre:
Rue de la Science 23,
B-1040 Brussels
t r s z CEN All rights of exploitation in any form and by any means reserved worldwide for CEN national Membersä Refä Noä EN
v s { t v sæ sã t r s z ESIST EN 419241-1:2018
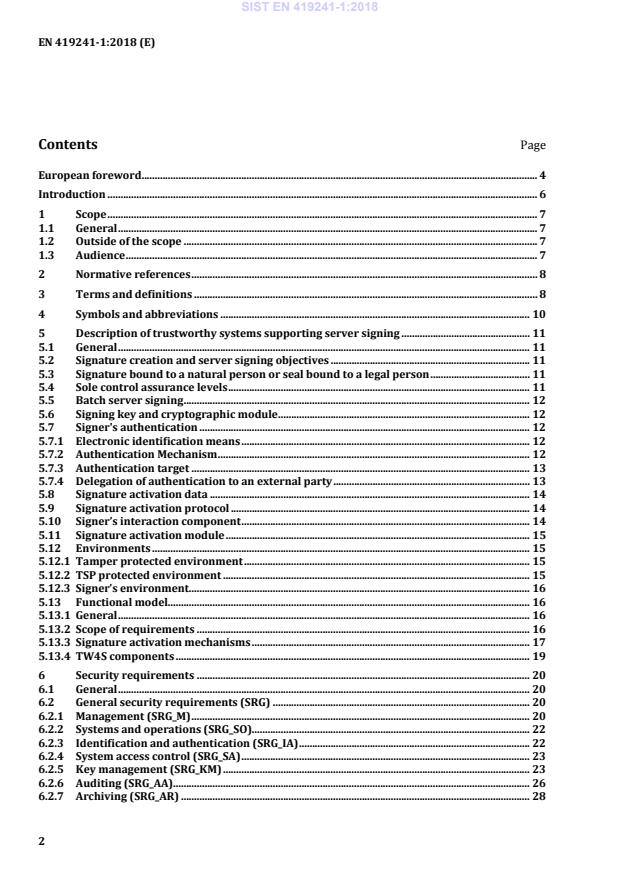
Requirements for electronic identification means, characteristics and design . 34 A.1 Enrolment . 34 A.1.1 Application and registration . 34 A.1.2 Identity proofing and verification (natural person) . 34 A.1.3 Identity proofing and verification (legal person) . 37 A.1.4 Binding between the electronic identification means of natural and legal persons . 39 A.2 Electronic identification means and authentication . 40 A.2.1 Electronic identification means characteristics and design . 40 A.2.2 Authentication mechanism . 41 Bibliography . 42
IEC Electropedia: available at http://www.electropedia.org/
ISO Online browsing platform: available at http://www.iso.org/obp 3.1 authentication provision of assurance in the identity of an entity [SOURCE: ISO/IEC 18014-2:2009] 3.2 authentication Factor piece of information and/or process used to authenticate or verify the identity of an entity [SOURCE: ISO/IEC 19790:2012] 3.3 data to be signed representation data formatted which is used to compute the digital signature value (e.g. hash value) [SOURCE: ETSI/TR 119 001:2016] 3.4 digital signature data unit appended to, or a cryptographic transformation of a data that allows a recipient of the data unit to prove the source and integrity of the data unit and protect against forgery e.g. by the recipient [SOURCE: ETSI/TR 119 001:2016] 3.5 eIDAS Regulation Regulation (EU) No 910/2014 of the European Parliament and of the Council on electronic identification and trust services for electronic transactions in the internal market and repealing Directive 1999/93/EC SIST EN 419241-1:2018
CC Common Criteria, ISO/IEC 15408, Evaluation criteria for IT security CEN Comité Européen de Normalization (European Committee for Standardization) DTBS/R Data To Be Signed Representation EAL Evaluation Assurance Level ETSI European Telecommunications Standards Institute ISO/IEC International Organization for Standardization / International Electrotechnical Commission ISSS Information Society Standardization System QSCD Qualified Electronic Signature (or Electronic Seal) creation device as defined in the eIDAS Regulation RA Registration Authority SAD Signature Activation Data SAM Signature Activation Module SAP Signature Activation Protocol SCA Signature Creation Application SCAL Sole Control Assurance Level SCDev Signature Creation Device SIC Signer’s Interaction Component SSA Server Signing Application TSP Trust Service Provider TW4S Trustworthy System Supporting Server Signing SIST EN 419241-1:2018
If the external party uses an electronic identification means issued under a notified scheme that is included in the list published by the Commission pursuant to Article 9 of the eIDAS [4] Regulation, there is no need to demonstrate the conformance to the required level, conformance to the regulatory requirements can be assumed. 5.7.4.3 SCAL2 The TSP SHALL ensure that the authentication process delegated to the external party meets the requirements specified in SRA_SAP.1.1. The TSP SHALL ensure that: — the external party fulfils all the relevant requirements of this standard and the requirements for registration according to the applicable regulatory requirements, or NOTE 1 In the context of the European Union, the applicable regulatory requirements are defined in REGULATION (EU) No 910/2014 [4]. — the authentication process delegated to the external party uses an electronic identification means issued under a notified scheme in accordance with the applicable regulatory requirements. NOTE 2 In the context of the European Union, the list of electronic identification means, issued under notified schemes, is published by the European Commission pursuant to Article 9 of REGULATION (EU) No 910/2014 [4].
Figure 1 — Scope of requirements NOTE The scope of requirements may be extended to an external party when using delegation of authentication (see 5.7.4). 5.13.3 Signature activation mechanisms 5.13.3.1 General This clause presents some suggested models for signature activation in order to create a digital signature. Any other architecture compliant with Clause 6 MAY be implemented. TW4S is typically used by a set of signers, each signer owning one or several signing keys and TW4S can include one or several SCDev to perform signature operations. The signing key can be securely stored outside the SCDev and loaded dynamically, provided that controls apply to ensure the same security on the signing key. Key loading/unloading mechanisms to be employed for protecting signing keys are outside the scope of this standard. 5.13.3.2 Signature activation for SCAL1 Signing key confidentiality and integrity are ensured by the SCDev. The SCDev can be activated by the SSA. The activation can remain for a given period and/or for a given number of signatures. The signing key activation requires that the signer has been authenticated by the SSA (see Figure 2). When the signer authentication succeeds, the corresponding signing key MAY be used for signature operation on behalf of signer within a certain time frame and/or a certain amount of signature operations. This allows the SSA to be used for bulk/batch signature purposes. SIST EN 419241-1:2018
Figure 2 —Signature activation system with SCAL1 NOTE This architecture may be extended to an external party when using delegation of authentication (see 5.7.4). This architecture can be used to create digital signature value (e.g. hash encrypted using the signer’s private key) with low assurance of control. 5.13.3.3 Signature activation for SCAL2 Signing key confidentiality and integrity are ensured by the remote SCDev. The remote SCDev is under control of the SSA. The remote SCDev participates in SAP and ensures that the signature operation is under the legitimate signer control. The SSA interfaces via a secure channel the SAM of the remote SCDev which verifies the SAD in order to activate the corresponding signing key (see Figure 3). The signer authentication can remain for a given period and/or for a given number of signatures. But SAD computation SHALL be done for each signature operation. The SAD MAY be linked to a set of DTBS/R, this allows the SSA to be used for bulk/batch signature purposes. Signer authentication can be done using a SSIC that is used to create a link between the signer and the signature as part of the SAD. The SAD uses is under the responsibility of the SAM: — If the SAD is generated by the SIC, it SHALL be transferred securely from the SIC to the SAM for verification. — If the SAD is not generated by the SIC, it SHALL be generated on/during a successful signer’s authentication using the SIC and be transferred securely to the SAM for verification. SIST EN 419241-1:2018
Figure 3 — Signature activation system with SCAL2 NOTE 1 This architecture may be extended to an external party when using delegation of authentication (see 5.7.4). NOTE 2 The scope of requirements may be extended to an external party when using delegation of authentication (see 5.7.4). This architecture can be used to create digital signature value (e.g. hash encrypted using the signer’s private key) with higher assurance of control. 5.13.4 TW4S components The core parts of a TW4S for which this standard specifies requirements are the set of functional components: — Signing key setup – to generate signing keys within the SCDev and assign them for use by authorized signers. — Signing key management – to delete, backup and restore signing keys within the SCDev. — Signer authentication – to authorize the use of signing key by the signer. — Digital signature creation – to interface the authorized signer in order to create the digital signature within the SCDev. In order to enhance level of assurance, additional components are mandatory to reach SCAL2: — The SIC – to create a link between the signer and the signature operation within the SAP. SIC MAY generate SAD in the signer’s environment.
The SAM provides a set of components: — SAD generation – to generate SAD in the tamper protected environment when the SAD is not generated by the SIC. — Signing key activation – to manage SAD verification and to activate the signing keys. — Signing key generation – to manage authentication factors bound to signing keys. 6 Security requirements 6.1 General This clause describes all requirements applicable to a server signing system in order to be regarded as a TW4S. Requirements in
...

Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...