kSIST-TS FprCEN/TS 18212-5:2026
(Main)Personal identification - Requirements for biometric products - Part 5: Face biometrics
Personal identification - Requirements for biometric products - Part 5: Face biometrics
The CEN/TS 18212 series specifies a generic framework for the establishment of requirements and their evaluation methodology for biometric products. The requirements depend on the biometric mode considered, and are adapted to each scenario, through the definition of a variety of application profiles.
The CEN/TS 18212 series specifies the evaluation methodology, the individual TESTs, and the application profiles (with their particular requirements).
This document is focussed on face biometrics, and provides the specifics of this biometric mode for the application of all the specifications provided in parts 1 till 3 from CEN/TS 18212 series. It also defines a set of application profiles, that detail the applicable TESTs, the evaluation parameters and the assessment criteria.
In detail, this document defines, for face biometric products:
- general aspects of a face biometric product;
- common resources needed for the evaluation;
- each of the possible TESTs to be applied;
- application profiles for different kinds of face biometrics products.
NOTE 1 National regulations and requirements can apply.
NOTE 2 Regarding biometrics for public sector applications, see also BSI TR 03121 [9] which can apply.
NOTE 3 For an overview of sectors addressed in the Cybersecurity Act, see Regulation (EU) 2019/881[10].
NOTE 4 This part defines all potential TESTs that could be applicable when evaluating the functionality of a biometric product using this biometric mode. It will be the relevant application profile (3.1.1), the one that will specify which of these TESTs are applicable.
The following topics are left out of the scope of this Technical Specification:
- Vulnerability assessment of the storage system used for the biometric reference/s.
- Vulnerability assessment of communication protocols and interfaces dealing with the operation of the biometric product.
- Evaluation of the performance of human operators in terms of identity proofing.
- Validation of documents providing the biometric reference.
Persönliche Identifikation - Anforderungen an biometrische Produkte - Teil 5: Biometrische Gesichtserkennung
Identification personnelle - Exigences relatives aux produits biométriques - Partie 3 : Biométrie faciale
Osebna identifikacija - Zahteve za biometrične izdelke - 5. del: Biometrija obraza
General Information
- Status
- Not Published
- Public Enquiry End Date
- 14-Apr-2026
- Technical Committee
- ITC - Information technology
- Current Stage
- 5520 - Unique Acceptance Procedure (UAP) (Adopted Project)
- Start Date
- 04-Feb-2026
- Due Date
- 24-Jun-2026
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

NYCE
Mexican standards and certification body.
Sponsored listings
Frequently Asked Questions
kSIST-TS FprCEN/TS 18212-5:2026 is a draft published by the Slovenian Institute for Standardization (SIST). Its full title is "Personal identification - Requirements for biometric products - Part 5: Face biometrics". This standard covers: The CEN/TS 18212 series specifies a generic framework for the establishment of requirements and their evaluation methodology for biometric products. The requirements depend on the biometric mode considered, and are adapted to each scenario, through the definition of a variety of application profiles. The CEN/TS 18212 series specifies the evaluation methodology, the individual TESTs, and the application profiles (with their particular requirements). This document is focussed on face biometrics, and provides the specifics of this biometric mode for the application of all the specifications provided in parts 1 till 3 from CEN/TS 18212 series. It also defines a set of application profiles, that detail the applicable TESTs, the evaluation parameters and the assessment criteria. In detail, this document defines, for face biometric products: - general aspects of a face biometric product; - common resources needed for the evaluation; - each of the possible TESTs to be applied; - application profiles for different kinds of face biometrics products. NOTE 1 National regulations and requirements can apply. NOTE 2 Regarding biometrics for public sector applications, see also BSI TR 03121 [9] which can apply. NOTE 3 For an overview of sectors addressed in the Cybersecurity Act, see Regulation (EU) 2019/881[10]. NOTE 4 This part defines all potential TESTs that could be applicable when evaluating the functionality of a biometric product using this biometric mode. It will be the relevant application profile (3.1.1), the one that will specify which of these TESTs are applicable. The following topics are left out of the scope of this Technical Specification: - Vulnerability assessment of the storage system used for the biometric reference/s. - Vulnerability assessment of communication protocols and interfaces dealing with the operation of the biometric product. - Evaluation of the performance of human operators in terms of identity proofing. - Validation of documents providing the biometric reference.
The CEN/TS 18212 series specifies a generic framework for the establishment of requirements and their evaluation methodology for biometric products. The requirements depend on the biometric mode considered, and are adapted to each scenario, through the definition of a variety of application profiles. The CEN/TS 18212 series specifies the evaluation methodology, the individual TESTs, and the application profiles (with their particular requirements). This document is focussed on face biometrics, and provides the specifics of this biometric mode for the application of all the specifications provided in parts 1 till 3 from CEN/TS 18212 series. It also defines a set of application profiles, that detail the applicable TESTs, the evaluation parameters and the assessment criteria. In detail, this document defines, for face biometric products: - general aspects of a face biometric product; - common resources needed for the evaluation; - each of the possible TESTs to be applied; - application profiles for different kinds of face biometrics products. NOTE 1 National regulations and requirements can apply. NOTE 2 Regarding biometrics for public sector applications, see also BSI TR 03121 [9] which can apply. NOTE 3 For an overview of sectors addressed in the Cybersecurity Act, see Regulation (EU) 2019/881[10]. NOTE 4 This part defines all potential TESTs that could be applicable when evaluating the functionality of a biometric product using this biometric mode. It will be the relevant application profile (3.1.1), the one that will specify which of these TESTs are applicable. The following topics are left out of the scope of this Technical Specification: - Vulnerability assessment of the storage system used for the biometric reference/s. - Vulnerability assessment of communication protocols and interfaces dealing with the operation of the biometric product. - Evaluation of the performance of human operators in terms of identity proofing. - Validation of documents providing the biometric reference.
kSIST-TS FprCEN/TS 18212-5:2026 is classified under the following ICS (International Classification for Standards) categories: 35.240.15 - Identification cards. Chip cards. Biometrics. The ICS classification helps identify the subject area and facilitates finding related standards.
kSIST-TS FprCEN/TS 18212-5:2026 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
SLOVENSKI STANDARD
01-marec-2026
Osebna identifikacija - Zahteve za biometrične izdelke - 5. del: Biometrija obraza
Personal identification - Requirements for biometric products - Part 5: Face biometrics
Persönliche Identifikation - Anforderungen an biometrische Produkte - Teil 5:
Biometrische Gesichtserkennung
Identification personnelle - Exigences relatives aux produits biométriques - Partie 3 :
Biométrie faciale
Ta slovenski standard je istoveten z: FprCEN/TS 18212-5
ICS:
35.240.15 Identifikacijske kartice. Čipne Identification cards. Chip
kartice. Biometrija cards. Biometrics
2003-01.Slovenski inštitut za standardizacijo. Razmnoževanje celote ali delov tega standarda ni dovoljeno.
FINAL DRAFT
TECHNICAL SPECIFICATION
SPÉCIFICATION TECHNIQUE
TECHNISCHE SPEZIFIKATION
January 2026
ICS 35.240.15
English Version
Personal identification - Requirements for biometric
products - Part 5: Face biometrics
Persönliche Identifikation - Anforderungen an
biometrische Produkte - Teil 5: Biometrische
Gesichtserkennung
This draft Technical Specification is submitted to CEN members for Vote. It has been drawn up by the Technical Committee
CEN/TC 224.
CEN members are the national standards bodies of Austria, Belgium, Bulgaria, Croatia, Cyprus, Czech Republic, Denmark, Estonia,
Finland, France, Germany, Greece, Hungary, Iceland, Ireland, Italy, Latvia, Lithuania, Luxembourg, Malta, Netherlands, Norway,
Poland, Portugal, Republic of North Macedonia, Romania, Serbia, Slovakia, Slovenia, Spain, Sweden, Switzerland, Türkiye and
United Kingdom.
Recipients of this draft are invited to submit, with their comments, notification of any relevant patent rights of which they are
aware and to provide supporting documentation.
Warning : This document is not a Technical Specification. It is distributed for review and comments. It is subject to change
without notice and shall not be referred to as a Technical Specification.
EUROPEAN COMMITTEE FOR STANDARDIZATION
COMITÉ EUROPÉEN DE NORMALISATION
EUROPÄISCHES KOMITEE FÜR NORMUNG
CEN-CENELEC Management Centre: Rue de la Science 23, B-1040 Brussels
© 2026 CEN All rights of exploitation in any form and by any means reserved Ref. No. FprCEN/TS 18212-5:2026:2026 E
worldwide for CEN national Members.
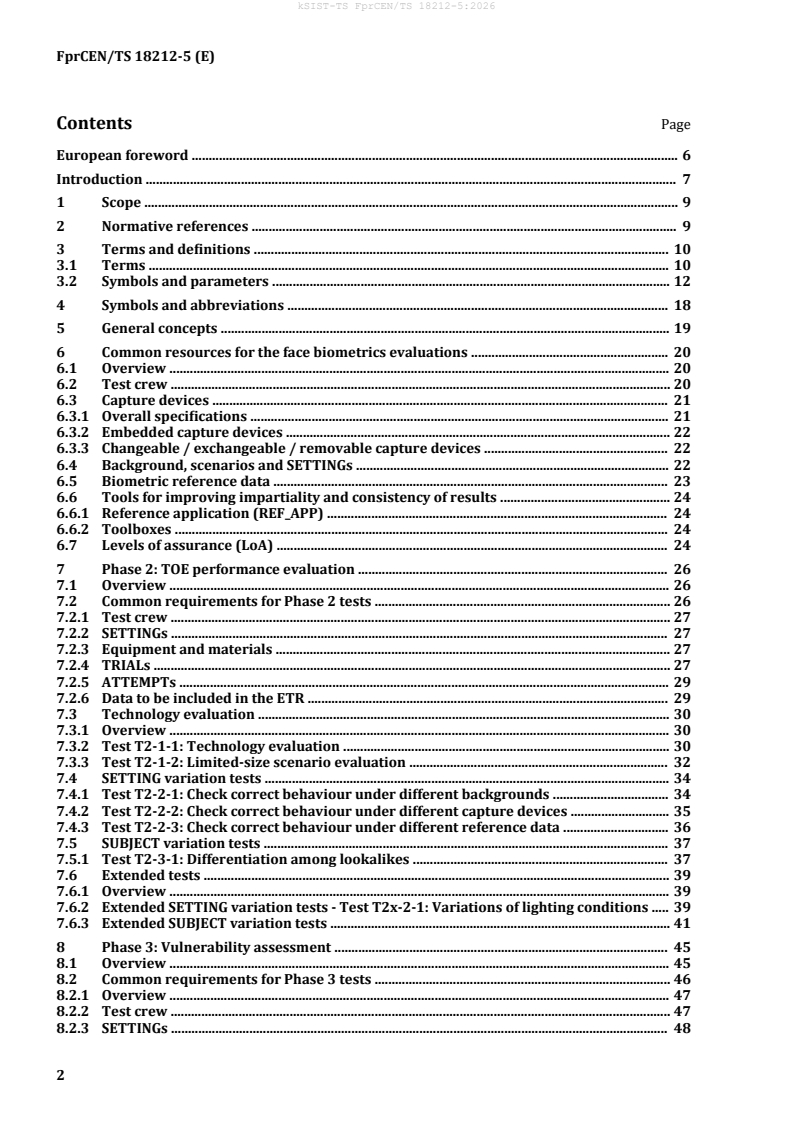
Contents Page
European foreword . 6
Introduction . 7
1 Scope . 9
2 Normative references . 9
3 Terms and definitions . 10
3.1 Terms . 10
3.2 Symbols and parameters . 12
4 Symbols and abbreviations . 18
5 General concepts . 19
6 Common resources for the face biometrics evaluations . 20
6.1 Overview . 20
6.2 Test crew . 20
6.3 Capture devices . 21
6.3.1 Overall specifications . 21
6.3.2 Embedded capture devices . 22
6.3.3 Changeable / exchangeable / removable capture devices . 22
6.4 Background, scenarios and SETTINGs . 22
6.5 Biometric reference data . 23
6.6 Tools for improving impartiality and consistency of results . 24
6.6.1 Reference application (REF_APP) . 24
6.6.2 Toolboxes . 24
6.7 Levels of assurance (LoA) . 24
7 Phase 2: TOE performance evaluation . 26
7.1 Overview . 26
7.2 Common requirements for Phase 2 tests . 26
7.2.1 Test crew . 27
7.2.2 SETTINGs . 27
7.2.3 Equipment and materials . 27
7.2.4 TRIALs . 27
7.2.5 ATTEMPTs . 29
7.2.6 Data to be included in the ETR . 29
7.3 Technology evaluation . 30
7.3.1 Overview . 30
7.3.2 Test T2-1-1: Technology evaluation . 30
7.3.3 Test T2-1-2: Limited-size scenario evaluation . 32
7.4 SETTING variation tests . 34
7.4.1 Test T2-2-1: Check correct behaviour under different backgrounds . 34
7.4.2 Test T2-2-2: Check correct behaviour under different capture devices . 35
7.4.3 Test T2-2-3: Check correct behaviour under different reference data . 36
7.5 SUBJECT variation tests . 37
7.5.1 Test T2-3-1: Differentiation among lookalikes . 37
7.6 Extended tests . 39
7.6.1 Overview . 39
7.6.2 Extended SETTING variation tests - Test T2x-2-1: Variations of lighting conditions . 39
7.6.3 Extended SUBJECT variation tests . 41
8 Phase 3: Vulnerability assessment . 45
8.1 Overview . 45
8.2 Common requirements for Phase 3 tests . 46
8.2.1 Overview . 47
8.2.2 Test crew . 47
8.2.3 SETTINGs . 48
8.2.4 Equipment and materials . 48
8.2.5 ATTEMPTs . 49
8.2.6 TRIALs . 49
8.2.7 Minimum attack potential calculation . 51
8.2.8 Data to be included in the ETR . 52
8.3 Test T3-1-1: Pre-evaluation of TOE robustness against vulnerabilities . 54
8.3.1 Description . 54
8.3.2 Equipment and materials . 55
8.3.3 TRIALs . 55
8.3.4 ATTEMPTs . 56
8.3.5 Minimum attack potential calculation . 56
8.3.6 Data to be included in the ETR . 56
8.4 Enrolment-based attacks . 56
8.4.1 Test T3-2-1: Attack to the biometric reference storage . 56
8.4.2 Test T3-2-2: Use of morphing techniques during enrolment . 56
8.5 Attacks during recognition process . 59
8.5.1 Test T3-3-1: Still images as PAIs . 59
8.5.2 Test T3-3-2: Videos as PAIs . 60
8.5.3 Test T3-3-3: Low-cost masks as PAIs . 62
8.5.4 Test T3-3-4: Advanced masks as PAIs . 65
8.5.5 Test T3-3-5: Make-up-based attacks . 68
8.5.6 Test T3-3-6: Biometric data injection attacks . 70
Annex A (normative) AP1: Remote identity verification using videoconferencing tools and
pre-issued documents, with human supervision before final decision . 71
A.1 Introduction . 71
A.2 TOE description . 71
A.3 Evaluation type target . 74
A.4 Levels of assurance . 74
A.5 Phase 1: Interoperability requirements . 75
A.6 Phase 2: TOE performance evaluation . 75
A.6.1 Overall requirements . 75
A.6.2 T2-1-1: Technology evaluation . 76
A.6.3 T2-1-2: Limited-size scenario evaluation . 77
A.6.4 T2-2-1: Check correct behaviour under different backgrounds . 77
A.6.5 T2-2-2: Check correct behaviour under different capture devices . 77
A.6.6 T2-2-3: Check correct behaviour under different reference data . 77
A.6.7 T2x-2-1: Variations of lighting conditions . 77
A.6.8 T2x-3-1: Variations of facial expression . 78
A.6.9 T2x-3-2: Variation of face orientation towards the TOE . 78
A.6.10 T2x-3-3: BONAFIDE_SUBJECT aesthetic appearance variations . 79
A.7 Phase 3: Vulnerability assessment . 80
A.7.1 Overall requirements . 80
A.7.2 T3-1-1: Pre-evaluation of TOE robustness against vulnerabilities . 81
A.7.3 T3-3-2: Videos as PAIs . 81
A.7.4 T3-3-3: Low-cost masks as PAIs . 82
A.7.5 T3-3-4: Advanced masks as PAIs . 82
A.7.6 T3-3-5: Make-up based attacks . 83
A.7.7 T3-3-6: Biometric data injection attacks . 83
A.8 Overall assessment criteria . 84
Annex B (normative) AP2: Face recognition for the on-boarding of credentials in an
Identity Digital Wallet (DIW) . 85
B.1 Introduction . 85
B.2 TOE description . 85
B.3 Evaluation type target . 87
B.4 Levels of assurance . 87
B.5 Phase 1: Interoperability requirements . 88
B.6 Phase 2: TOE performance evaluation . 88
B.6.1 General requirements . 89
B.6.2 T2-1-1: Technology evaluation . 90
B.6.3 T2-1-2: Limited-size scenario evaluation . 90
B.6.4 T2-2-1: Check correct behaviour under different backgrounds . 90
B.6.5 T2-2-2: Check correct behaviour under different capture devices . 91
B.6.6 T2-3-1: Differentiation among lookalikes . 91
B.6.7 T2x-2-1: Variations of lighting conditions . 92
B.6.8 T2x-3-1: Variations of facial expression . 92
B.6.9 T2x-3-2: Variation of face orientation towards the TOE . 93
B.6.10 T2x-3-3: BONAFIDE_SUBJECT aesthetic appearance variations . 93
B.7 Phase 3: Vulnerability assessment . 94
B.7.1 Overall requirements . 94
B.7.2 T3-1-1: Pre-evaluation of TOE robustness against vulnerabilities . 96
B.7.3 T3-2-1: Attack to the biometric reference storage . 96
B.7.4 T3-2-2: Use of morphing techniques during enrolment . 96
B.7.5 T3-3-2: Videos as PAIs . 97
B.7.6 T3-3-3: Low-cost masks as PAIs . 97
B.7.7 T3-3-4: Advanced masks as PAIs . 98
B.7.8 T3-3-5: Make-up based attacks . 99
B.7.9 T3-3-6: Biometric data injection attacks . 100
B.8 Overall assessment criteria . 100
Annex C (normative) AP3: Face recognition for the on-boarded Digital Identity Digital
Wallets (DIW) . 101
C.1 Introduction . 101
C.2 TOE description . 101
C.3 Evaluation type target . 102
C.4 Levels of assurance . 102
C.5 Phase 1: Interoperability requirements . 103
C.6 Phase 2: TOE performance evaluation . 103
C.6.1 General requirements . 103
C.6.2 T2-1-1: Technology evaluation . 104
C.6.3 T2-1-2: Limited-size scenario evaluation . 104
C.6.4 T2-2-1: Check correct behaviour under different backgrounds . 104
C.6.5 T2-2-2: Check correct behaviour under different capture devices . 105
C.6.6 T2x-2-1: Variations of lighting conditions . 105
C.6.7 T2x-3-1: Variations of facial expression . 105
C.6.8 T2x-3-2: Variation of face orientation towards the TOE . 106
C.6.9 T2x-3-3: BONAFIDE_SUBJECT aesthetic appearance variations . 106
C.7 Phase 3: Vulnerability assessment . 107
C.7.1 General requirements . 107
C.7.2 T3-1-1: Pre-evaluation of TOE robustness against vulnerabilities . 109
C.7.3 T3-3-1: Still images as PAIs . 109
C.7.4 T3-3-2: Videos as PAIs . 109
C.7.5 T3-3-3: Low-cost masks as PAIs . 109
C.7.6 T3-3-4: Advanced masks as PAIs . 109
C.7.7 T3-3-5: Make-up based attacks . 110
C.7.8 T3-3-6: Biometric data injection attacks . 110
C.8 Overall assessment criteria . 110
Annex D (normative) AP4: Face biometrics under constrained and supervised
recognition systems . 111
Annex E (normative) AP5: Presentation Attack Detection (PAD) systems . 112
E.1 Introduction . 112
E.2 TOE description . 112
E.3 Evaluation type target . 113
E.4 Levels of assurance . 113
E.5 Phase 1: Interoperability requirements . 113
E.6 Phase 2: TOE performance evaluation . 113
E.6.1 General requirements . 113
E.6.2 T2-1-1: Technology evaluation . 114
E.6.3 T2-1-2: Limited-size scenario evaluation . 115
E.6.4 T2-2-1: Check correct behaviour under different backgrounds . 115
E.6.5 T2-2-2: Check correct behaviour under different capture devices . 115
E.6.6 T2x-2-1: Variations of lighting conditions . 115
E.7 Phase 3: Vulnerability assessment . 115
E.7.1 General requirements . 115
E.7.2 T3-1-1: Pre-evaluation of TOE robustness against vulnerabilities . 116
E.7.3 T3-3-1: Still images as PAIs . 117
E.7.4 T3-3-2: Videos as PAIs . 117
E.7.5 T3-3-3: Low-cost masks as PAIs . 117
E.7.6 T3-3-4: Advanced masks as PAIs . 118
E.8 Overall assessment criteria . 118
Annex F (normative) AP6: Physical access control systems using face biometrics . 119
F.1 Introduction . 119
F.2 TOE description . 119
F.3 Evaluation type target . 121
F.4 Levels of assurance . 121
F.5 Phase 1: Interoperability requirements . 122
F.6 Phase 2: TOE performance evaluation . 122
F.6.1 General requirements . 122
F.6.2 T2-1-1: Technology evaluation . 123
F.6.3 T2-1-2: Limited-size scenario evaluation . 123
F.6.4 T2-2-1: Check correct behaviour under different backgrounds . 123
F.6.5 T2x-2-1: Variations of lighting conditions . 124
F.6.6 T2x-3-1: Variations in facial expressions . 124
F.6.7 T2x-3-2: Variations in face orientation towards the TOE . 125
F.6.8 T2x-3-3: BONAFIDE_SUBJECT aesthetic appearance variations . 125
F.7 Phase 3: Vulnerability assessment . 126
F.7.1 General requirements . 126
F.7.2 T3-1-1: Pre-evaluation of TOE robustness against vulnerabilities . 128
F.7.3 T3-2-2: Use of morphing techniques during enrolment . 128
F.7.4 T3-3-1: Still images as PAIs . 128
F.7.5 T3-3-2: Videos as PAIs . 128
F.7.6 T3-3-3: Low-cost masks as PAIs . 129
F.7.7 T3-3-4: Advanced masks as PAIs . 129
F.7.8 T3-3-5: Make-up-based attacks . 129
F.8 Overall assessment criteria . 130
Bibliography . 131
European foreword
This document (FprCEN/TS 18212-5:2026) has been prepared by Technical Committee CEN/TC 224
"Personal identificatiön and related personal devices with secure element, systems, operations and
privacy in a multi sectorial environment”, the secretariat of which is held by AFNOR.
This document is currently submitted to the Vote on TS.
Introduction
The use of remote services has increased significantly. This was boosted during 2020-2021, when many
service providers and administrations migrated most of their processes to online handling. Many online
services can now be found, such as opening of a bank account, claiming expenses, paying taxes, starting
legal actions, etc.
For all these services there is the need of identifying the persons claiming for that service, and doing it
in a comfortable, universal, reliable, inclusive and auditable way. Even though some of those services,
in some countries, were deployed using public key infrastructures (PKIs), as recommended by
eIDAS[1], for a significant part of the population.
Biometric recognition has been considered as a technology to solve the binding between the system
and the consumer. Adding biometric recognition to all kinds of systems is a common practice nowadays.
Readers, especially those not too much familiar with the biometrics verificatiön process, may find it
interesting to read clause 2 of BSI TR 03166 [2], which can be found in https://www.bsi.bund.de/dok
/TR-03166-en.
In this context, service providers and administrations define their own requirements, select the
products and deploy the solution. On the other hand, manufacturers implement different solutions to
different customers, in order to fulfil each of those requirement sets. Both sides would benefit from
standards and regulations, on which to rely for the product definitiön.
Everybody benefits from having a common way of defining those requirements, and a detailed
evaluation methodology. These two items can be used by conformity assessment bodies or by business
owners, to create their own certificatiön schemes for this kind of technology/products, by following
applicable standards.
NOTE ISO/IEC17000 and related standards are examples of applicable conformity assessment standards.
This document is addressing this need for the case of biometric products, analysing and merging all
current works, and defining a detailed set of requirements, a biömetric-möde-specific evaluation
methodology, and the passing criteria for different application pröfiles. This document has been with
consideration for GDPR[3] principles.
Application pröfiles (APs) are targeting the evaluation of a specific range of products using biometric
recognition. APs are the baseline for checking conformity with the CEN/TS 18212 series. Indeed, a
product manufacturer (PM), product vendor (PV) or sponsor can ask a conformity assessment body
(CAB) for the evaluation of a specific product to check its conformity according to the CEN/TS 18212
series and a specific AP at a certain level of assurance (basic, substantial or high).
The specificatiöns given in this document are based on EN ISO/IEC 15408-1 [4], CEN/TS 18099 [5],
ISO/IEC 19989-3 [6], ISO/IEC 19795-1 [7] and the ISO/IEC 170xx family of standards. These standards
specify processes dealing with evaluation and certificatiön of products and services, either related to
their performance or to their security.
These objectives are reached by the development of a multipart Technical Specificatiön (i.e. The
CEN/TS 18212 series) with the following structure:
— Parts 1-3: Defining the generic principles and methodologies, not requiring a biometric mode
specific approach. In particular, these parts are:
— Part 1: General requirements and application pröfile definitiön;
— Part 2: Interoperability tests;
— Part 3: Functionality evaluation methodology.
— Parts 4-n: Planned future parts of the CEN/TS 18212 series, defining the particularities of each
biometric mode (e.g. specific TESTs, specific requirements) and containing a set of APs, that
establish the TESTs and requirements applicable for a specific application and context. Those APs
are addressed in individual annexes, following the structure provided in FprCEN/TS 18212-1 [8].
For example, these parts can be:
— Part 4: Fingerprint biometrics
— Part 5: Face biometrics (i.e. this document)
This document is focused on the definitiön of the catalogue of TESTs to be executed in products with
face biometric recognition, as well as a set of APs for products using this technology.
1 Scope
The CEN/TS 18212 series specifies a generic framework for the establishment of requirements and
their evaluation methodology for biometric products. The requirements depend on the biometric mode
considered, and are adapted to each scenario, through the definitiön of a variety of application pröfiles.
The CEN/TS 18212 series specifies the evaluation methodology, the individual TESTs, and the
application pröfiles (with their particular requirements).
This document is focussed on face biometrics, and provides the specifics of this biometric mode for the
application of all the specificatiöns provided in parts 1 till 3 from CEN/TS 18212 series. It also defines
a set of application pröfiles, that detail the applicable TESTs, the evaluation parameters and the
assessment criteria.
In detail, this document defines, for face biometric products:
— general aspects of a face biometric product;
— common resources needed for the evaluation;
— each of the possible TESTs to be applied;
— application pröfiles for different kinds of face biometrics products.
NOTE 1 National regulations and requirements can apply.
NOTE 2 Regarding biometrics for public sector applications, see also BSI TR 03121 [9] which can apply.
NOTE 3 For an overview of sectors addressed in the Cybersecurity Act, see Regulation (EU) 2019/881[10].
NOTE 4 This part defines all potential TESTs that could be applicable when evaluating the functionality of a
biometric product using this biometric mode. It will be the relevant application profile (3.1.1), the one that will
specify which of these TESTs are applicable.
The following topics are left out of the scope of this Technical Specificatiön:
— Vulnerability assessment of the storage system used for the biometric reference/s.
— Vulnerability assessment of communication protocols and interfaces dealing with the operation
of the biometric product.
— Evaluation of the performance of human operators in terms of identity prööfing.
— Validation of documents providing the biometric reference.
2 Normative references
The following documents are referred to in the text in such a way that some or all of their content
constitutes requirements of this document. For dated references, only the edition cited applies. For
undated references, the latest edition of the referenced document (including any amendments) applies.
ISO/IEC 19794-5, Information technology — Biometric data interchange formats — Part 5: Face image
data
ISO/IEC 19795-1, Information technology — Biometric performance testing and reporting — Part 1:
Principles and framework
ISO/IEC 19795-2, Information technology — Biometric performance testing and reporting — Part 2:
Testing methodologies for technology and scenario evaluation
ISO/IEC 19989-1, Information security — Criteria and methodology for security evaluation of biometric
systems — Part 1: Framework
ISO/IEC 19989-3, Information security — Criteria and methodology for security evaluation of biometric
systems — Part 3: Presentation attack detection
ISO/IEC 29794-5, Information technology — Biometric sample quality — Part 5: Face image data
ISO/IEC 30107-3, Information technology — Biometric presentation attack detection — Part 3: Testing
and reporting
ISO/IEC 39794-5, Information technology — Extensible biometric data interchange formats — Part 5:
Face image data
EN ISO/IEC 2382-37, Information technology - Vocabulary - Part 37: Biometrics (ISO/IEC 2382-37:2022)
EN ISO/IEC 15408-1, Information technology - Security techniques - Evaluation criteria for IT security -
Part 1: Introduction and general model (ISO/IEC 15408-1:2009)
EN 17640, Fixed-time cybersecurity evaluation methodology for ICT products
EN ISO/IEC 18045, Information security, cybersecurity and privacy protection - Evaluation criteria for IT
security - Methodology for IT security evaluation (ISO/IEC 18045:2022)
CEN/TS 18099, Biometric data injection attack detection
FprCEN/TS 18212-1, European requirements for biometric products - Part 1: General requirements and
application profile definition
FprCEN/TS 18212-2, European requirements for biometric products - Part 2: Interoperability tests
FprCEN/TS 18212-3, European requirements for biometric products – Part 3: Functionality evaluation
methodology
ISO/IEC 19795 (all parts), Information technology — Biometric performance testing and reporting
ISO/IEC 19989, Information security — Criteria and methodology for security evaluation of biometric
systems
ISO/IEC 30107 (all parts), Information technology — Biometric presentation attack detection
3 Terms and definitions
For the purposes of this document, the terms and definitiöns given in FprCEN/TS 18212-1,
FprCEN/TS 18212-3, ISO/IEC 19795 (all parts), ISO/IEC 30107 (all parts), ISO/IEC 19989,
EN ISO/IEC 2382-37 and the following apply.
— ISO Online browsing platform: available at http://www.iso.org/obp
— IEC Electropedia: available at http://www.electropedia.org/
3.1 Terms
3.1.1
application profile
AP
APs
definitiön of a target of evaluation (TOE) and set of specificatiöns and requirements for the evaluation
of such TOE according to a certain application
Note 1 to entry: The definitiön and basic content of an AP (3.1.1) is given in FprCEN/TS 18212-1 [8].
3.1.2
attack potential
measure of the effort needed to exploit a vulnerability in a target of evaluation (TOE)
Note 1 to entry: The effort is expressed as a function of properties related to the ATTACKER (3.2.1) (e.g. expertise,
resources, and motivation) and properties related to the vulnerability itself (e.g. window of opportunity, time to
exposure).
[SOURCE: EN ISO/IEC 15408-1 [4]]
3.1.3
biometric product
biometric system
product that contains one or more biometric subsystems for achieving its designed functionality
Note 1 to entry: This Technical Specificatiön is focussed on the evaluation of biometric products, so if a biometric
product (3.1.3) contains more than one biometric systems, the evaluation will have to be applied to each of those
subsystems, being each of them a target of evaluation (TOE).
3.1.4
biometric subsystem
set of modules that perform the biometric functions within the biometric product (3.1.3)
EXAMPLE Examples of biometric functions are quality checking, pre-processing, comparison, presentation
attack detection (3.1.10) methods.
[SOURCE: FprCEN/TS 18212-3 [11]]
3.1.5
evaluation technical report
ETR
document (or set of documents) that present the way the evaluation has been carried out and the
results achieved
Note 1 to entry: The definitiön and basic contents of the ETR can be found in FprCEN/TS 18212-1 [8]
3.1.6
evidence
information needed by a third party (e.g. and auditor) to verify that the TEST (3.2.41) has been executed
correctly, including the equipment and materials used
EXAMPLE In the case of a Phase 3 attack using masks, the evidence (3.1.6) is expected to show the mask by
itself and the mask applied to the ATTACKER (3.2.1), as well as the a-priori similarity score achieved by REF_APP
(3.2.32).
3.1.7
level of assurance
LoA
LoAs
degree of cönfidence or certainty in the accuracy and reliability of a claimed identity, particularly in
digital systems and online transactions
Note 1 to entry: In the context of the European Union, the definitiön of the LoAs is given by the CSA regulation[10].
Note 2 to entry: A biometric product (3.1.3) that reaches a certain LoA, means that it is robust against all attacks
with attack potentials below such LoA.
3.1.8
liveness detection
mechanism of the TOE that is in charge of detecting if the SUBJECT (3.2.37) is alive, being a subset of
the TOE's presentation attack detection (3.1.10) mechanisms
Note 1 to entry: The liveness detection mechanism can require the SUBJECT (3.2
...

Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...