ISO/IEC 9594-8:2008
(Main)Information technology — Open Systems Interconnection — The Directory: Public-key and attribute certificate frameworks — Part 8:
Information technology — Open Systems Interconnection — The Directory: Public-key and attribute certificate frameworks — Part 8:
ISO/IEC 9594-8:2008 addresses some of the security requirements in the areas of authentication and other security services through the provision of a set of frameworks upon which full services can be based. Specifically, it defines frameworks for: Public-key certificates; Attribute certificates; Authentication services. The public-key certificate framework defined in ISO/IEC 9594-8:2008 includes definition of the information objects for Public Key Infrastructure (PKI), including public-key certificates, and Certificate Revocation List (CRL). The attribute certificate framework includes definition of the information objects for Privilege Management Infrastructure (PMI), including attribute certificates, and Attribute Certificate Revocation List (ACRL). ISO/IEC 9594-8:2008 also provides the framework for issuing, managing, using and revoking certificates. An extensibility mechanism is included in the defined formats for both certificate types and for all revocation list schemes. ISO/IEC 9594-8:2008 also includes a set of standard extensions for each, which is expected to be generally useful across a number of applications of PKI and PMI. The schema components (including object classes, attribute types and matching rules) for storing PKI and PMI objects in the Directory are included in ISO/IEC 9594-8:2008. Other elements of PKI and PMI, beyond these frameworks, such as key and certificate management protocols, operational protocols, additional certificate and CRL extensions, are expected to be defined by other standards bodies (e.g. ISO/TC 68 and IETF). The authentication scheme defined in ISO/IEC 9594-8:2008 is generic and can be applied to a variety of applications and environments. The Directory makes use of public-key certificates and attribute certificates, and the framework for the Directory's use of these facilities is also defined in ISO/IEC 9594-8:2008. Public-key technology, including certificates, is used by the Directory to enable strong authentication, signed and/or encrypted operations, and for storage of signed and/or encrypted data in the Directory. Attribute certificates can be used by the Directory to enable rule-based access control. Although the framework for these is provided in this Specification, the full definition of the Directory's use of these frameworks, and the associated services provided by the Directory and its components, is supplied in the complete set of Directory Specifications. ISO/IEC 9594-8:2008, in the Authentication services framework, also: specifies the form of authentication information held by the Directory; describes how authentication information may be obtained from the Directory; states the assumptions made about how authentication information is formed and placed in the Directory; defines three ways in which applications may use this authentication information to perform authentication and describes how other security services may be supported by authentication. ISO/IEC 9594-8:2008 describes two levels of authentication: simple authentication, using a password as a verification of claimed identity; and strong authentication, involving credentials formed using cryptographic techniques. While simple authentication offers some limited protection against unauthorized access, only strong authentication should be used as the basis for providing secure services. It is not intended to establish this as a general framework for authentication, but it can be of general use for applications that consider these techniques adequate. Authentication (and other security services) can only be provided within the context of a defined security policy. It is a matter for users of an application to define their own security policy, which may be constrained by the services provided by a standard. It is a matter for standards-defining applications that use the authentication framework to specify the protocol exchanges which need to be performed in order to achieve authentication base
Technologies de l'information — Interconnexion de systèmes ouverts (OSI) — L'annuaire: Cadre général des certificats de clé publique et d'attribut — Partie 8:
General Information
- Status
- Withdrawn
- Publication Date
- 14-Dec-2008
- Withdrawal Date
- 14-Dec-2008
- Current Stage
- 9599 - Withdrawal of International Standard
- Start Date
- 25-Feb-2014
- Completion Date
- 14-Feb-2026
Relations
- Effective Date
- 09-Feb-2026
- Effective Date
- 06-Sep-2025
- Effective Date
- 31-Aug-2013
- Effective Date
- 18-Dec-2008
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

NYCE
Mexican standards and certification body.
Sponsored listings
Frequently Asked Questions
ISO/IEC 9594-8:2008 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information technology — Open Systems Interconnection — The Directory: Public-key and attribute certificate frameworks — Part 8:". This standard covers: ISO/IEC 9594-8:2008 addresses some of the security requirements in the areas of authentication and other security services through the provision of a set of frameworks upon which full services can be based. Specifically, it defines frameworks for: Public-key certificates; Attribute certificates; Authentication services. The public-key certificate framework defined in ISO/IEC 9594-8:2008 includes definition of the information objects for Public Key Infrastructure (PKI), including public-key certificates, and Certificate Revocation List (CRL). The attribute certificate framework includes definition of the information objects for Privilege Management Infrastructure (PMI), including attribute certificates, and Attribute Certificate Revocation List (ACRL). ISO/IEC 9594-8:2008 also provides the framework for issuing, managing, using and revoking certificates. An extensibility mechanism is included in the defined formats for both certificate types and for all revocation list schemes. ISO/IEC 9594-8:2008 also includes a set of standard extensions for each, which is expected to be generally useful across a number of applications of PKI and PMI. The schema components (including object classes, attribute types and matching rules) for storing PKI and PMI objects in the Directory are included in ISO/IEC 9594-8:2008. Other elements of PKI and PMI, beyond these frameworks, such as key and certificate management protocols, operational protocols, additional certificate and CRL extensions, are expected to be defined by other standards bodies (e.g. ISO/TC 68 and IETF). The authentication scheme defined in ISO/IEC 9594-8:2008 is generic and can be applied to a variety of applications and environments. The Directory makes use of public-key certificates and attribute certificates, and the framework for the Directory's use of these facilities is also defined in ISO/IEC 9594-8:2008. Public-key technology, including certificates, is used by the Directory to enable strong authentication, signed and/or encrypted operations, and for storage of signed and/or encrypted data in the Directory. Attribute certificates can be used by the Directory to enable rule-based access control. Although the framework for these is provided in this Specification, the full definition of the Directory's use of these frameworks, and the associated services provided by the Directory and its components, is supplied in the complete set of Directory Specifications. ISO/IEC 9594-8:2008, in the Authentication services framework, also: specifies the form of authentication information held by the Directory; describes how authentication information may be obtained from the Directory; states the assumptions made about how authentication information is formed and placed in the Directory; defines three ways in which applications may use this authentication information to perform authentication and describes how other security services may be supported by authentication. ISO/IEC 9594-8:2008 describes two levels of authentication: simple authentication, using a password as a verification of claimed identity; and strong authentication, involving credentials formed using cryptographic techniques. While simple authentication offers some limited protection against unauthorized access, only strong authentication should be used as the basis for providing secure services. It is not intended to establish this as a general framework for authentication, but it can be of general use for applications that consider these techniques adequate. Authentication (and other security services) can only be provided within the context of a defined security policy. It is a matter for users of an application to define their own security policy, which may be constrained by the services provided by a standard. It is a matter for standards-defining applications that use the authentication framework to specify the protocol exchanges which need to be performed in order to achieve authentication base
ISO/IEC 9594-8:2008 addresses some of the security requirements in the areas of authentication and other security services through the provision of a set of frameworks upon which full services can be based. Specifically, it defines frameworks for: Public-key certificates; Attribute certificates; Authentication services. The public-key certificate framework defined in ISO/IEC 9594-8:2008 includes definition of the information objects for Public Key Infrastructure (PKI), including public-key certificates, and Certificate Revocation List (CRL). The attribute certificate framework includes definition of the information objects for Privilege Management Infrastructure (PMI), including attribute certificates, and Attribute Certificate Revocation List (ACRL). ISO/IEC 9594-8:2008 also provides the framework for issuing, managing, using and revoking certificates. An extensibility mechanism is included in the defined formats for both certificate types and for all revocation list schemes. ISO/IEC 9594-8:2008 also includes a set of standard extensions for each, which is expected to be generally useful across a number of applications of PKI and PMI. The schema components (including object classes, attribute types and matching rules) for storing PKI and PMI objects in the Directory are included in ISO/IEC 9594-8:2008. Other elements of PKI and PMI, beyond these frameworks, such as key and certificate management protocols, operational protocols, additional certificate and CRL extensions, are expected to be defined by other standards bodies (e.g. ISO/TC 68 and IETF). The authentication scheme defined in ISO/IEC 9594-8:2008 is generic and can be applied to a variety of applications and environments. The Directory makes use of public-key certificates and attribute certificates, and the framework for the Directory's use of these facilities is also defined in ISO/IEC 9594-8:2008. Public-key technology, including certificates, is used by the Directory to enable strong authentication, signed and/or encrypted operations, and for storage of signed and/or encrypted data in the Directory. Attribute certificates can be used by the Directory to enable rule-based access control. Although the framework for these is provided in this Specification, the full definition of the Directory's use of these frameworks, and the associated services provided by the Directory and its components, is supplied in the complete set of Directory Specifications. ISO/IEC 9594-8:2008, in the Authentication services framework, also: specifies the form of authentication information held by the Directory; describes how authentication information may be obtained from the Directory; states the assumptions made about how authentication information is formed and placed in the Directory; defines three ways in which applications may use this authentication information to perform authentication and describes how other security services may be supported by authentication. ISO/IEC 9594-8:2008 describes two levels of authentication: simple authentication, using a password as a verification of claimed identity; and strong authentication, involving credentials formed using cryptographic techniques. While simple authentication offers some limited protection against unauthorized access, only strong authentication should be used as the basis for providing secure services. It is not intended to establish this as a general framework for authentication, but it can be of general use for applications that consider these techniques adequate. Authentication (and other security services) can only be provided within the context of a defined security policy. It is a matter for users of an application to define their own security policy, which may be constrained by the services provided by a standard. It is a matter for standards-defining applications that use the authentication framework to specify the protocol exchanges which need to be performed in order to achieve authentication base
ISO/IEC 9594-8:2008 is classified under the following ICS (International Classification for Standards) categories: 35.100.70 - Application layer. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 9594-8:2008 has the following relationships with other standards: It is inter standard links to CEN/TS 16439:2013, ISO/IEC 9594-8:2005/Cor 4:2012, ISO/IEC 9594-8:2014, ISO/IEC 9594-8:2005. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
ISO/IEC 9594-8:2008 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 9594-8
Sixth edition
2008-12-15
Information technology — Open Systems
Interconnection — The Directory: Public-
key and attribute certificate frameworks
Technologies de l'information — Interconnexion de systèmes ouverts
(OSI) — L'annuaire: Cadre général des certificats de clé publique et
d'attribut
Reference number
©
ISO/IEC 2008
PDF disclaimer
This PDF file may contain embedded typefaces. In accordance with Adobe's licensing policy, this file may be printed or viewed but
shall not be edited unless the typefaces which are embedded are licensed to and installed on the computer performing the editing. In
downloading this file, parties accept therein the responsibility of not infringing Adobe's licensing policy. The ISO Central Secretariat
accepts no liability in this area.
Adobe is a trademark of Adobe Systems Incorporated.
Details of the software products used to create this PDF file can be found in the General Info relative to the file; the PDF-creation
parameters were optimized for printing. Every care has been taken to ensure that the file is suitable for use by ISO member bodies. In
the unlikely event that a problem relating to it is found, please inform the Central Secretariat at the address given below.
© ISO/IEC 2008
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized in any form or by any means,
electronic or mechanical, including photocopying and microfilm, without permission in writing from either ISO at the address below or
ISO's member body in the country of the requester.
ISO copyright office
Case postale 56 • CH-1211 Geneva 20
Tel. + 41 22 749 01 11
Fax + 41 22 749 09 47
E-mail copyright@iso.org
Web www.iso.org
Published by ISO in 2009
Published in Switzerland
ii © ISO/IEC 2008 – All rights reserved
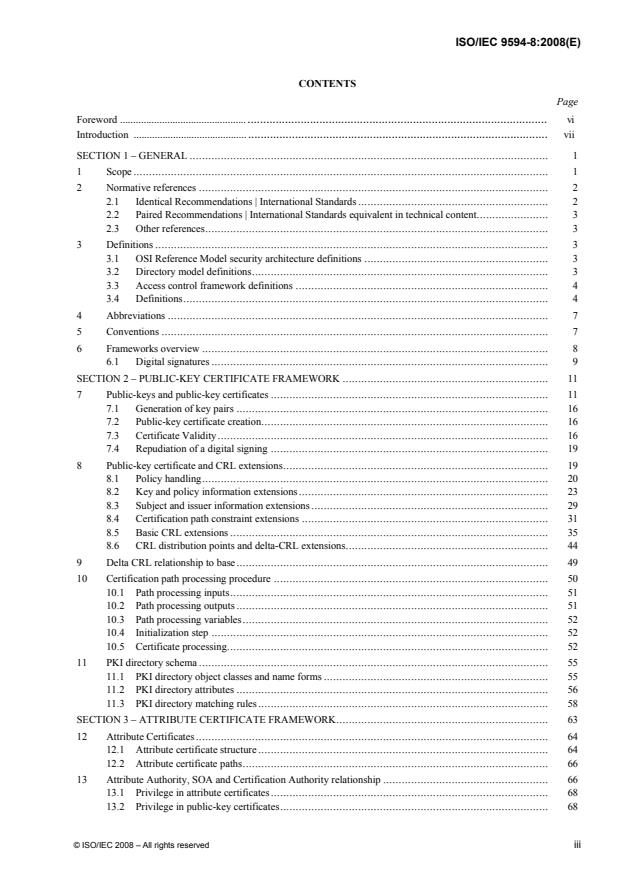
CONTENTS
Page
Foreword . vi
Introduction . vii
SECTION 1 – GENERAL . 1
1 Scope. 1
2 Normative references . 2
2.1 Identical Recommendations | International Standards. 2
2.2 Paired Recommendations | International Standards equivalent in technical content. 3
2.3 Other references. 3
3 Definitions . 3
3.1 OSI Reference Model security architecture definitions . 3
3.2 Directory model definitions. 3
3.3 Access control framework definitions . 4
3.4 Definitions. 4
4 Abbreviations . 7
5 Conventions . 7
6 Frameworks overview . 8
6.1 Digital signatures . 9
SECTION 2 – PUBLIC-KEY CERTIFICATE FRAMEWORK . 11
7 Public-keys and public-key certificates . 11
7.1 Generation of key pairs . 16
7.2 Public-key certificate creation. 16
7.3 Certificate Validity. 16
7.4 Repudiation of a digital signing . 19
8 Public-key certificate and CRL extensions. 19
8.1 Policy handling. 20
8.2 Key and policy information extensions. 23
8.3 Subject and issuer information extensions. 29
8.4 Certification path constraint extensions . 31
8.5 Basic CRL extensions . 35
8.6 CRL distribution points and delta-CRL extensions. 44
9 Delta CRL relationship to base. 49
10 Certification path processing procedure . 50
10.1 Path processing inputs. 51
10.2 Path processing outputs . 51
10.3 Path processing variables. 52
10.4 Initialization step . 52
10.5 Certificate processing. 52
11 PKI directory schema . 55
11.1 PKI directory object classes and name forms . 55
11.2 PKI directory attributes . 56
11.3 PKI directory matching rules. 58
SECTION 3 – ATTRIBUTE CERTIFICATE FRAMEWORK. 63
12 Attribute Certificates. 64
12.1 Attribute certificate structure. 64
12.2 Attribute certificate paths. 66
13 Attribute Authority, SOA and Certification Authority relationship . 66
13.1 Privilege in attribute certificates. 68
13.2 Privilege in public-key certificates. 68
© ISO/IEC 2008 – All rights reserved iii
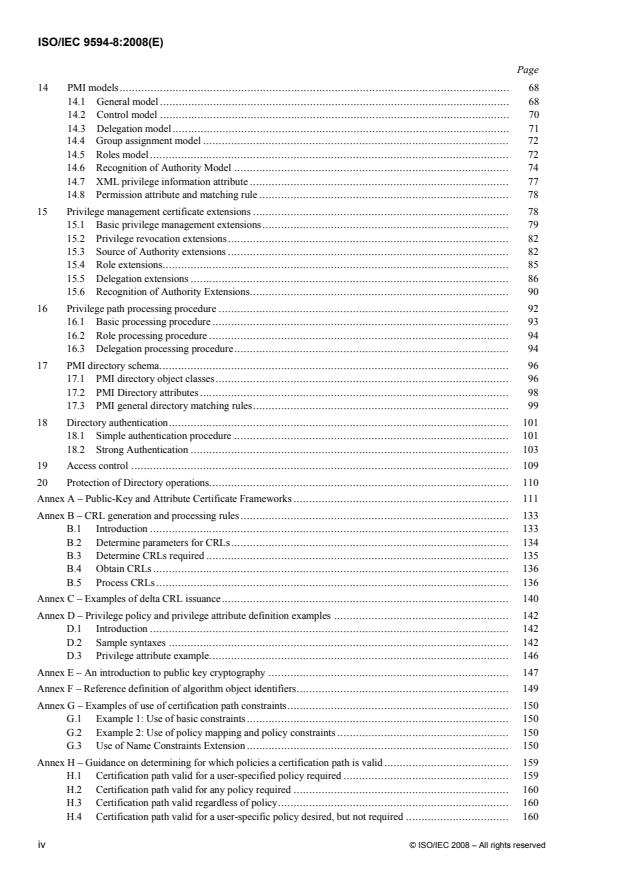
Page
14 PMI models. 68
14.1 General model. 68
14.2 Control model . 70
14.3 Delegation model. 71
14.4 Group assignment model . 72
14.5 Roles model. 72
14.6 Recognition of Authority Model . 74
14.7 XML privilege information attribute . 77
14.8 Permission attribute and matching rule . 78
15 Privilege management certificate extensions . 78
15.1 Basic privilege management extensions. 79
15.2 Privilege revocation extensions. 82
15.3 Source of Authority extensions . 82
15.4 Role extensions. 85
15.5 Delegation extensions . 86
15.6 Recognition of Authority Extensions. 90
16 Privilege path processing procedure . 92
16.1 Basic processing procedure . 93
16.2 Role processing procedure . 94
16.3 Delegation processing procedure. 94
17 PMI directory schema. 96
17.1 PMI directory object classes. 96
17.2 PMI Directory attributes. 98
17.3 PMI general directory matching rules. 99
18 Directory authentication. 101
18.1 Simple authentication procedure . 101
18.2 Strong Authentication . 103
19 Access control . 109
20 Protection of Directory operations. 110
Annex A – Public-Key and Attribute Certificate Frameworks . 111
Annex B – CRL generation and processing rules. 133
B.1 Introduction . 133
B.2 Determine parameters for CRLs. 134
B.3 Determine CRLs required . 135
B.4 Obtain CRLs. 136
B.5 Process CRLs. 136
Annex C – Examples of delta CRL issuance. 140
Annex D – Privilege policy and privilege attribute definition examples . 142
D.1 Introduction . 142
D.2 Sample syntaxes . 142
D.3 Privilege attribute example. 146
Annex E – An introduction to public key cryptography . 147
Annex F – Reference definition of algorithm object identifiers. 149
Annex G – Examples of use of certification path constraints. 150
G.1 Example 1: Use of basic constraints. 150
G.2 Example 2: Use of policy mapping and policy constraints . 150
G.3 Use of Name Constraints Extension. 150
Annex H – Guidance on determining for which policies a certification path is valid. 159
H.1 Certification path valid for a user-specified policy required . 159
H.2 Certification path valid for any policy required . 160
H.3 Certification path valid regardless of policy. 160
H.4 Certification path valid for a user-specific policy desired, but not required . 160
iv © ISO/IEC 2008 – All rights reserved
Page
Annex I – Key usage certificate extension issues. 161
Annex J – External ASN.1 modules. 162
Annex K – Use of Protected Passwords for Bind operations . 169
Annex L – Alphabetical list of information item definitions. 170
Annex M – Amendments and corrigenda . 173
© ISO/IEC 2008 – All rights reserved v
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are members of
ISO or IEC participate in the development of International Standards through technical committees
established by the respective organization to deal with particular fields of technical activity. ISO and IEC
technical committees collaborate in fields of mutual interest. Other international organizations, governmental
and non-governmental, in liaison with ISO and IEC, also take part in the work. In the field of information
technology, ISO and IEC have established a joint technical committee, ISO/IEC JTC 1.
International Standards are drafted in accordance with the rules given in the ISO/IEC Directives, Part 2.
The main task of the joint technical committee is to prepare International Standards. Draft International
Standards adopted by the joint technical committee are circulated to national bodies for voting. Publication as
an International Standard requires approval by at least 75 % of the national bodies casting a vote.
Attention is drawn to the possibility that some of the elements of this document may be the subject of patent
rights. ISO and IEC shall not be held responsible for identifying any or all such patent rights.
Subcommittee SC 6, Telecommunications and information exchange between systems, in collaboration with
ITU-T. The identical text is published as ITU-T Rec. X.509 (11/2008).
This sixth edition cancels and replaces the fifth edition (ISO/IEC 9594-8:2005), which has been technically
revised.
ISO/IEC 9594 consists of the following parts, under the general title Information technology — Open Systems
Interconnection — The Directory:
⎯ Part 1: Overview of concepts, models and services
⎯ Part 2: Models
⎯ Part 3: Abstract service definition
⎯ Part 4: Procedures for distributed operation
⎯ Part 5: Protocol specifications
⎯ Part 6: Selected attribute types
⎯ Part 7: Selected object classes
⎯ Part 8: Public-key and attribute certificate frameworks
⎯ Part 9: Replication
⎯ Part 10: Use of systems management for administration of the Directory
vi © ISO/IEC 2008 – All rights reserved
Introduction
This Recommendation | International Standard, together with other Recommendations | International Standards, has
been produced to facilitate the interconnection of information processing systems to provide directory services. A set of
such systems, together with the directory information which they hold, can be viewed as an integrated whole, called the
Directory. The information held by the Directory, collectively known as the Directory Information Base (DIB), is
typically used to facilitate communication between, with or about objects such as application-entities, people, terminals
and distribution lists.
The Directory plays a significant role in Open Systems Interconnection, whose aim is to allow, with a minimum of
technical agreement outside of the interconnection standards themselves, the interconnection of information processing
systems:
– from different manufacturers;
– under different managements;
– of different levels of complexity; and
– of different ages.
Many applications have requirements for security to protect against threats to the communication of information.
Virtually all security services are dependent upon the identities of the communicating parties being reliably known, i.e.,
authentication.
This Recommendation | International Standard defines a framework for public-key certificates. That framework
includes specification of data objects used to represent the certificates themselves as well as revocation notices for
issued certificates that should no longer be trusted. The public-key certificate framework defined in this
Recommendation | International Standard, while it defines some critical components of a Public-key Infrastructure
(PKI), it does not define a PKI in its entirety. However, this Recommendation | International Standard provides the
foundation upon which full PKIs and their specifications would be built.
Similarly, this Recommendation | International Standard defines a framework for attribute certificates. That framework
includes specification of data objects used to represent the certificates themselves as well as revocation notices for
issued certificates that should no longer be trusted. The attribute certificate framework defined in this
Recommendation | International Standard, while it defines some critical components of a Privilege Management
Infrastructure (PMI), does not define a PMI in its entirety. However, this Recommendation | International Standard
provides the foundation upon which full PMIs and their specifications would be built.
Information objects for holding PKI and PMI objects in the Directory and for comparing presented values with stored
values are also defined.
This Recommendation | International Standard also defines a framework for the provision of authentication services by
the Directory to its users.
This Recommendation | International Standard provides the foundation frameworks upon which industry profiles can be
defined by other standards groups and industry forums. Many of the features defined as optional in these frameworks
may be mandated for use in certain environments through profiles. This sixth edition technically revises and enhances,
but does not replace, the fifth edition of this Recommendation | International Standard. Implementations may still claim
conformance to the fifth edition. However, at some point, the fifth edition will not be supported (i.e., reported defects
will no longer be resolved). It is recommended that implementations conform to this sixth edition as soon as possible.
This sixth edition specifies versions 1, 2 and 3 of public-key certificates and versions 1 and 2 of certificate revocation
lists. This edition also specifies version 2 of attribute certificates.
The extensibility function was added in an earlier edition with version 3 of the public-key certificate and with version 2
of the certificate revocation list and was incorporated into the attribute certificate from its initial inception. This
function is specified in clause 7. It is anticipated that any enhancements to this edition can be accommodated using this
function and avoid the need to create new versions
Annex A, which is an integral part of this Recommendation | International Standard, provides the ASN.1 modules
which contain all of the definitions associated with the frameworks.
Annex B, which is an integral part of this Recommendation | International Standard, provides rules for generating and
processing Certificate Revocation Lists.
Annex C, which is not an integral part of this Recommendation | International Standard, provides examples of delta-
CRL issuance.
© ISO/IEC 2008 – All rights reserved vii
Annex D, which is not an integral part of this Recommendation | International Standard, provides examples of privilege
policy syntaxes and privilege attributes.
Annex E, which is not an integral part of this Recommendation | International Standard, is an introduction to public-key
cryptography.
Annex F, which is an integral part of this Recommendation | International Standard, defines object identifiers assigned
to authentication and encryption algorithms, in the absence of a formal register.
Annex G, which is not an integral part of this Recommendation | International Standard, contains examples of the use of
certification path constraints.
Annex H, which is not an integral part of this Recommendation | International Standard, provides guidance for PKI
enabled applications on the processing of certificate policy while in the certificate path validation process.
Annex I, which is not an integral part of this Recommendation | International Standard, provides guidance on the use of
the contentCommitment bit in the keyUsage certificate extension.
Annex J, which is not an integral part of this Recommendation | International Standard, includes extracts of external
ASN.1 modules referenced by this Recommendation | International Standard.
Annex K, which is not an integral part of this Recommendation | International Standard, provides a suggested technique
for Bind protected password.
Annex L, which is not an integral part of this Recommendation | International Standard, contains an alphabetical list of
information item definitions in this Recommendation | International Standard.
Annex M, which is not an integral part of this Recommendation | International Standard, lists the amendments and
defect reports that have been incorporated to form this edition of this Recommendation | International Standard.
viii © ISO/IEC 2008 – All rights reserved
INTERNATIONAL STANDARD
ITU-T RECOMMENDATION
Information technology – Open systems interconnection –
The Directory: Public-key and attribute certificate frameworks
SECTION 1 – GENERAL
1 Scope
This Recommendation | International Standard addresses some of the security requirements in the areas of
authentication and other security services through the provision of a set of frameworks upon which full services can be
based. Specifically, this Recommendation | International Standard defines frameworks for:
– Public-key certificates;
– Attribute certificates;
– Authentication services.
The public-key certificate framework defined in this Recommendation | International Standard includes definition of the
information objects for Public Key Infrastructure (PKI), including public-key certificates, and Certificate Revocation
List (CRL). The attribute certificate framework includes definition of the information objects for Privilege Management
Infrastructure (PMI), including attribute certificates, and Attribute Certificate Revocation List (ACRL). This
Recommendation | International Standard also provides the framework for issuing, managing, using and revoking
certificates. An extensibility mechanism is included in the defined formats for both certificate types and for all
revocation list schemes. This Recommendation | International Standard also includes a set of standard extensions for
each, which is expected to be generally useful across a number of applications of PKI and PMI. The schema
components (including object classes, attribute types and matching rules) for storing PKI and PMI objects in the
Directory, are included in this Recommendation | International Standard. Other elements of PKI and PMI, beyond these
frameworks, such as key and certificate management protocols, operational protocols, additional certificate and CRL
extensions are expected to be defined by other standards bodies (e.g., ISO TC 68, IETF, etc.).
The authentication scheme defined in this Recommendation | International Standard is generic and may be applied to a
variety of applications and environments.
The Directory makes use of public-key certificates and attribute certificates, and the framework for the Directory's use
of these facilities is also defined in this Recommendation | International Standard. Public-key technology, including
certificates, is used by the Directory to enable strong authentication, signed and/or encrypted operations, and for storage
of signed and/or encrypted data in the Directory. Attribute certificates can be used by the Directory to enable rule-based
access control. Although the framework for these is provided in this Recommendation | International Standard, the full
definition of the Directory's use of these frameworks, and the associated services provided by the Directory and its
components is supplied in the complete set of X.500 ITU-T series of Recommendation | ISO/IEC 9594 (all parts).
This Recommendation | International Standard, in the Authentication services framework, also:
– specifies the form of authentication information held by the Directory;
– describes how authentication information may be obtained from the Directory;
– states the assumptions made about how authentication information is formed and placed in the Directory;
– defines three ways in which applications may use this authentication information to perform
authentication and describes how other security services may be supported by authentication.
This Recommendation | International Standard describes two levels of authentication: simple authentication, using a
password as a verification of claimed identity; and strong authentication, involving credentials formed using
cryptographic techniques. While simple authentication offers some limited protection against unauthorized access, only
strong authentication should be used as the basis for providing secure services. It is not intended to establish this as a
general framework for authentication, but it can be of general use for applications which consider these techniques
adequate.
Authentication (and other security services) can only be provided within the context of a defined security policy. It is a
matter for users of an application to define their own security policy which may be constrained by the services provided
by a standard.
ITU-T Rec. X.509 (11/2008) 1
It is a matter for standards-defining applications which use the authentication framework to specify the protocol
exchanges which need to be performed in order to achieve authentication based upon the authentication information
obtained from the Directory. The protocol used by applications to obtain credentials from the Directory is the Directory
Access Protocol (DAP), specified in ITU-T Rec. X.519 | ISO/IEC 9594-5.
2 Normative references
The following Recommendations and International Standards contain provisions which, through reference in this text,
constitute provisions of this Recommendation | International Standard. At the time of publication, the editions indicated
were valid. All Recommendations and Standards are subject to revision, and parties to agreements based on this
Recommendation | International Standard are encouraged to investigate the possibility of applying the most recent
edition of the Recommendations and Standards listed below. Members of IEC and ISO maintain registers of currently
valid International Standards. The Telecommunication Standardization Bureau of the ITU maintains a list of currently
valid ITU-T Recommendations.
2.1 Identical Recommendations | International Standards
– ITU-T Recommendation X.411 (1999) | ISO/IEC 10021-4:2003, Information technology – Message
Handling Systems (MHS) – Message transfer system: Abstract service definition and procedures.
– ITU-T Recommendation X.500 (2008) | ISO/IEC 9594-1:2008, Information technology – Open Systems
Interconnection – The Directory: Overview of concepts, models and services.
– ITU-T Recommendation X.501 (2008) | ISO/IEC 9594-2:2008, Information technology – Open Systems
Interconnection – The Directory: Models.
– ITU-T Recommendation X.511 (2008) | ISO/IEC 9594-3:2008, Information technology – Open Systems
Interconnection – The Directory: Abstract service definition.
– ITU-T Recommendation X.518 (2008) | ISO/IEC 9594-4:2008, Information technology – Open Systems
Interconnection – The Directory: Procedures for distributed operation.
– ITU-T Recommendation X.519 (2008) | ISO/IEC 9594-5:2008, Information technology – Open Systems
Interconnection – The Directory: Protocol specifications.
– ITU-T Recommendation X.520 (2008) | ISO/IEC 9594-6:2008, Information technology – Open Systems
Interconnection – The Directory: Selected attribute types.
– ITU-T Recommendation X.521 (2008) | ISO/IEC 9594-7:2008, Information technology – Open Systems
Interconnection – The Directory: Selected object classes.
– ITU-T Recommendation X.525 (2008) | ISO/IEC 9594-9:2008, Information technology – Open Systems
Interconnection – The Directory: Replication.
– ITU-T Recommendation X.530 (2008) | ISO/IEC 9594-10:2008, Information technology – Open Systems
Interconnection – The Directory: Use of systems management for administration of the Directory.
– ITU-T Recommendation X.660 (2008) | ISO/IEC 9834-1:2008, Information technology – Open Systems
Interconnection – Procedures for the operation of OSI Registration Authorities: General procedures,
and top arcs of the ASN.1 Object Identifier tree.
– ITU-T Recommendation X.680 (2008) | ISO/IEC 8824-1:2008, Information technology – Abstract
Syntax Notation One (ASN.1): Specification of basic notation.
– ITU-T Recommendation X.681 (2008) | ISO/IEC 8824-2:2008, Information technology – Abstract
Syntax Notation One (ASN.1): Information object specification.
– ITU-T Recommendation X.682 (2008) | ISO/IEC 8824-3:2008, Information technology – Abstract
Syntax Notation One (ASN.1): Constraint specification.
– ITU-T Recommendation X.683 (2008) | ISO/IEC 8824-4:2008, Information technology – Abstract
Syntax Notation One (ASN.1): Parameterization of ASN.1 specifications.
– ITU-T Recommendation X.690 (2008) | ISO/IEC 8825-1:2008, Information technology – ASN.1
encoding rules: Specification of Basic Encoding Rules (BER), Canonical Encoding Rules (CER) and
Distinguished Encoding Rules (DER).
– ITU-T Recommendation X.691 (2008) | ISO/IEC 8825-2:2008, Information technology – ASN.1
encoding rules: Specification of Packed Encoding Rules (PER).
2 ITU-T Rec. X.509 (11/2008)
– ITU-T Recommendation X.812 (1995) | ISO/IEC 10181-3:1996, Information technology – Open Systems
Interconnection – Security frameworks for open systems: Access control framework.
– ITU-T Recommendation X.813 (1996) | ISO/IEC 10181-4:1997, Information technology – Open Systems
Interconnection – Security frameworks for open systems: Non-repudiation framework.
2.2 Paired Recommendations | International Standards equivalent in technical content
– CCITT Recommendation X.800 (1991), Security Architecture for Open Systems Interconnection for
CCITT applications.
ISO 7498-2:1989, Information processing systems – Open Systems Interconnection – Basic Reference
Model – Part 2: Security Architecture.
2.3 Other references
– IETF RFC 5280 (2008), Internet X.509 Public Key Infrastructure Certificate and Certificate Revocation
List (CRL) Profile.
3 Definitions
For the purposes of this Recommendation | International Standard, the following definitions apply.
3.1 OSI Reference Model security architecture definitions
The following terms are defined in CCITT Rec. X.800 | ISO 7498-2:
a) asymmetric (encipherment);
b) authentication exchange;
c) authentication information;
d) confidentiality;
e) credentials;
f) cryptography;
g) data origin authentication;
h) decipherment;
i) digital signature;
j) encipherment;
k) key;
l) password;
m) peer-entity authentication;
n) symmetric (encipherment).
3.2 Directory model definitions
The following terms are defined in ITU-T Rec. X.501 | ISO/IEC 9594-2:
a) attribute;
b) Directory Information Base;
c) Directory Information Tree;
d) Directory System Agent;
e) Directory User Agent;
f) distinguished name;
g) entry;
h) object;
i) root.
ITU-T Rec. X.509 (11/2008) 3
3.3 Access control framework definitions
The following terms are defined in ITU-T Rec. X.812 | ISO/IEC 10181-3:
a) Access control Decision Function (ADF);
b) Access control Enforcement Function (AEF).
3.4 Definitions
The following terms are defined in this Recommendation | International Standard:
3.4.1 attribute certificate (AC): A data structure, digitally signed by an Attribute Authority, that binds some
attribute values with identification information about its holder.
3.4.2 Attribute Authority (AA): An authority which assigns privileges by issuing attribute certificates.
3.4.3 attribute authority revocation list (AARL): A revocation list containing a list of references to attribute
certificates issued to AAs that are no longer considered valid by the issuing authority.
3.4.4 attribute certificate revocation list (ACRL): A revocation list containing a list of references to attribute
certificates that are no longer considered valid by the issuing authority.
3.4.5 authentication token; (token): Information conveyed during a strong authentication exchange, which can be
used to authenticate its sender.
3.4.6 authority: An entity, responsible for the issuance of certificates. Two types are defined in this
Recommendation | International Standard; certification authority which issues public-key certificates and attribute
authority which issues attribute certificates.
3.4.7 authority certificate: A certificate issued to an authority (e.g., either to a certification authority or to an
attribute authority).
3.4.8 base CRL: A CRL that is used as the foundation in the generation of a dCRL.
3.4.9 CA-certificate: A certificate for one CA issued by another CA.
3.4.10 certificate policy: A named set of rules that indicates the applicability of a certificate to a particular
community and/or class of application with common security requirements. For example, a particular certificate policy
might indicate applicability of a type of certificate to the authentication of electronic data interchange transactions for
the trading of goods within a given price range.
3.4.11 certification practice statement (CPS): A statement of the practices that a CA employs in issuing
certificates.
3.4.12 certificate revocation list (CRL): A signed list indicating a set of certificates that are no longer considered
valid by the certificate issuer. In addition to the generic term CRL, some specific CRL types are defined for CRLs that
cover particular scopes.
3.4.13 certificate user: An entity that needs to know, with certainty, the attributes and/or public key of another
entity.
3.4.14 certificate serial number: An integer value, unique within the issuing authority, which is unambiguously
associated with a certificate issued by that authority.
3.4.15 certificate-using system: An implementation of those functions defined in this Recommendation |
International Standard that are used by a certificate-user.
3.4.16 certificate validation: The process of ensuring that a certificate was valid at a given time, including possibly
the construction and processing of a certification path, and ensuring that all certificates in that path were valid (i.e., were
not expired or revoked) at that given time.
3.4.17 certification authority (CA): An authority trusted by one or more users to create and assign public-key
certificates. Optionally the certification authority may create the users' keys.
3.4.18 certification authority revocation list (CARL): A revocation list containing a list of public-key certificates
issued to certification authorities that are no longer considered valid by the certificate issuer.
3.4.19 certification path: An ordered sequence of public-key certificates of objects in the DIT which, together with
the public key of the initial object in the path, can be processed to obtain that of the final object in the path.
4 ITU-T Rec. X.509 (11/2008)
3.4.20 CRL distribution point: A directory entry or other distribution source for CRLs; a CRL distributed through a
CRL distribution point may contain revocation entries for only a subset of the full set of certificates issued by one CA
or may contain revocation entries for multiple CAs.
3.4.21 cross-certificate: A public-key or attribute certificate where the issuer and the subject/holder are different
CAs or AAs respectively. CAs and AAs issue cross-certificates to other CAs or AAs respectively as a mechanism to
authorize the subject CA's existence (e.g., in a strict hierarchy) or to recognize the existence of the subject CA or holder
AA (e.g., in a distributed trust model). The cross-certificate structure is used for both of these.
3.4.22 cryptographic system, cryptosystem: A collection of transformations from plain text into cipher text and
vice versa, the particular transformation(s) to be used being selected by keys. The transformations are normally defined
by a mathematical algorithm.
3.4.23 data confidentiality: This service can be used to provide for protection of data from unauthorized disclosure.
The data confidentiality service is supported by the authentication framework. It can be used to protect against data
interception.
3.4.24 delegation: Conveyance of privilege from one entity that holds such privilege, to another entity.
3.4.25 delegation path: An ordered sequence of certificates which, together with authentication of a privilege
asserter's identity can be processed to verify the authenticity of an asserter's privilege.
3.4.26 delta-CRL (dCRL): A partial revocation list that only contains entries for certificates that have had their
revocation status changed since the issuance of the referenced base CRL.
3.4.27 end entity: Either a public-key certificate subject that uses its private key for purposes other than signing
certificates, or an attribute certificate holder that uses its attributes to gain access to a resource, or an entity that is a
relying party.
3.4.28 end-entity attribute certificate: An attribute certificate issued to an end-entity.
3.4.29 end-entity attribute certificate revocation list (EARL): A revocation list containing a list of attribute
certificates issued to holders that are not also AAs that are no longer considered valid by the certificate issuer.
3.4.30 end-entity certificate: An attribute or public-key certificate issued to an end-entity.
3.4.31 end-entity public-key certificate: A public-key certificate issued to an end-entity.
3.4.32 end-entity public-key certificate revocation list (EPRL): A revocation list containing a list of public-key
certificates issued to subjects that are not also CAs, that are no longer considered valid by the certificate issuer.
3.4.33 environmental variables: Those aspects of policy required for an authorization decision, that are not
contained within static structures, but are available through some local means to a privilege verifier (e.g., time of day or
current account balance).
3.4.34 full CRL: A complete revocation list that contains entries for all certificates that have been revoked for the
given scope.
3.4.35 hash function: A (mathematical) function which maps values from a large (possibly very large) domain into a
smaller range. A "good" hash function is such that the results of applying the function to a (large) set of values in the
domain will be evenly distributed (and apparently at random) over the range.
3.4.36 holder: An entity to whom some privilege has been delegated either directly from the Source of Authority or
indirectly through another Attribute Authority.
3.4.37 indirect CRL (iCRL): A revocation list that at least contains revocation information about certificates issued
by authorities other than that which issued this CRL.
3.4.38 key agreement: A method for negotiating a key value on-line without transferring the key, even in an
encrypted form, e.g., the Diffie-Hellman technique (see ISO/IEC 11770-1 for more information on key agreement
mechanisms).
3.4.39 object method: An action that can be invoked on a resource (e.g., a file system may have read, write and
execute object methods).
3.4.40 one-way function: A (mathematical) function f which is easy to compute, but which for a general value y in
the range, it is computationally difficult to find a value x in the domain such that f(x) = y. There may be a few values y
for which finding x is not computationally difficult.
3.4.41 policy decision point (PDP): The point where policy decisions are made (synonymous with ADF).
ITU-T Rec. X.509 (11/2008) 5
-----------------
...
Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...